xBOM Detailed Setup Guide¶
This guide walks you through setting up xBOM with your AccuKnox tenant and generating BOM files.
What is xBOM¶
xBOM is an umbrella term covering SBOM (software dependencies), CBOM (cryptographic assets), and AIBOM (AI/ML models). Each maps a different layer of the supply chain to track risk, meet compliance requirements like EO 14028 and the EU AI Act, and respond to vulnerabilities faster.
Prerequisites¶
- Access to AccuKnox UI
knoxctlbinary installed on your system
Step 1: Create Project and Classifier¶
-
Log in to the AccuKnox UI
-
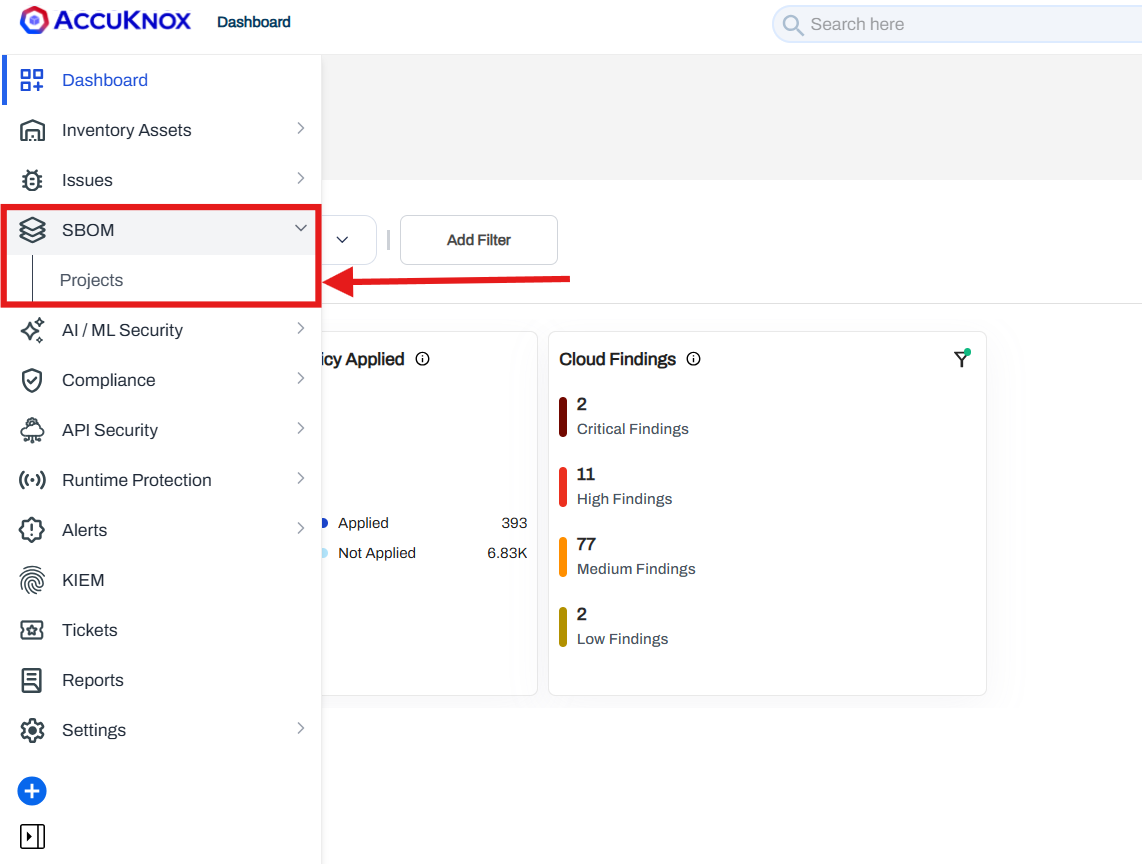
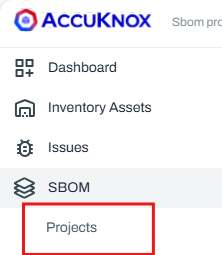
Navigate to SBOM > Projects
-
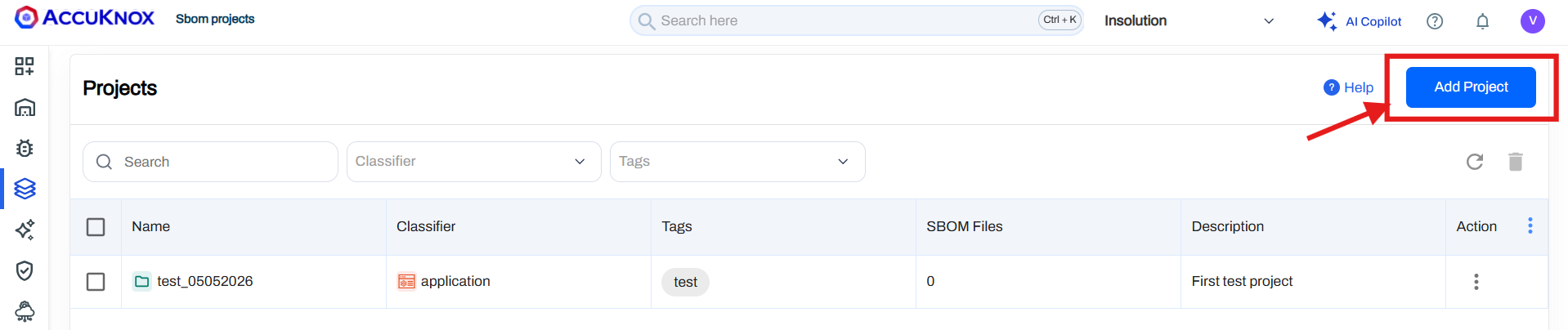
Click Add Project
-
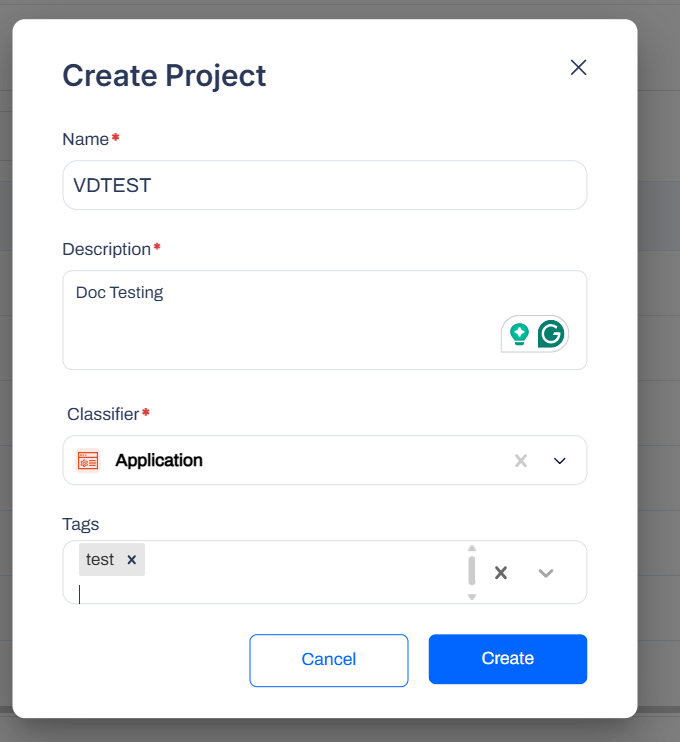
Fill in the following fields:
- Project name
- Description
- Classifier
-
Click on the Create button.
Step 2: Create Labels¶
Set up your labels for organising projects:
-
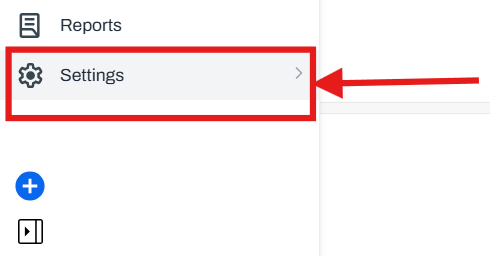
In the AccuKnox UI, navigate to Settings
-
Go to Labels
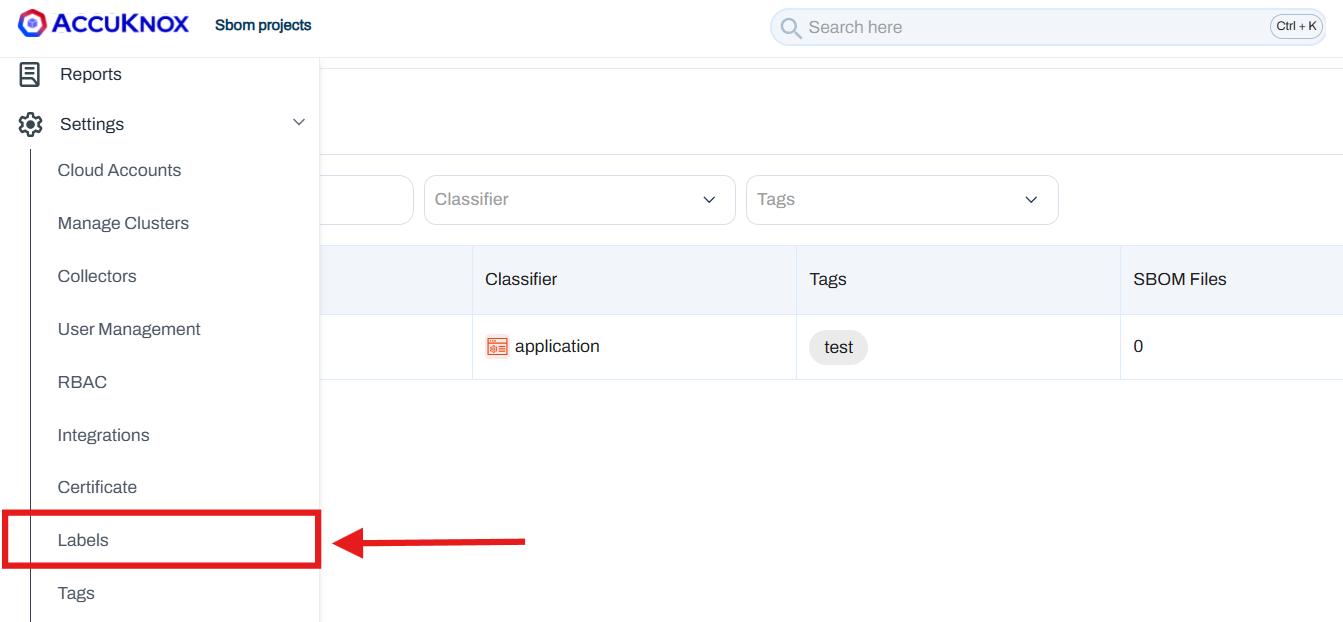
-
Click the Label+ button
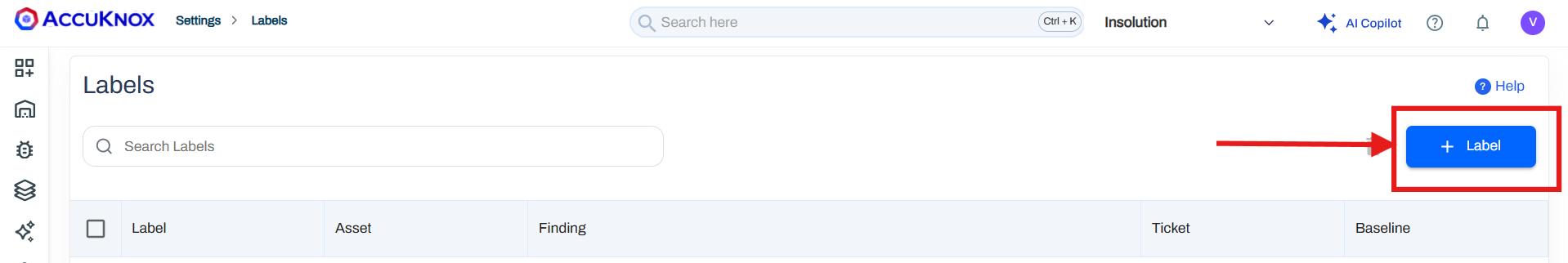
-
Create the labels you need for organising your projects
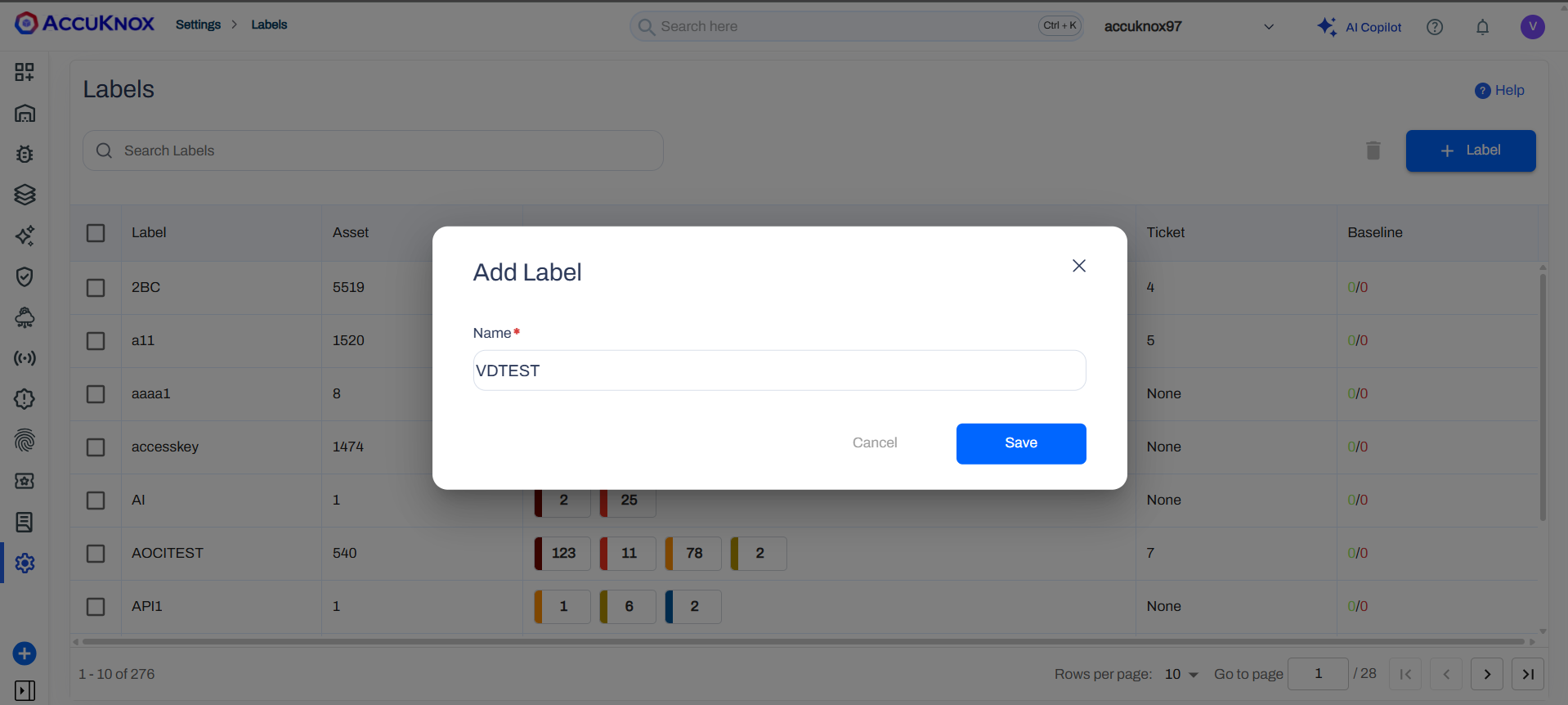
-
Save your label configuration.
Reference: How to Create Labels
Step 3: Generate Access Key¶
-
Navigate to Settings > User Management
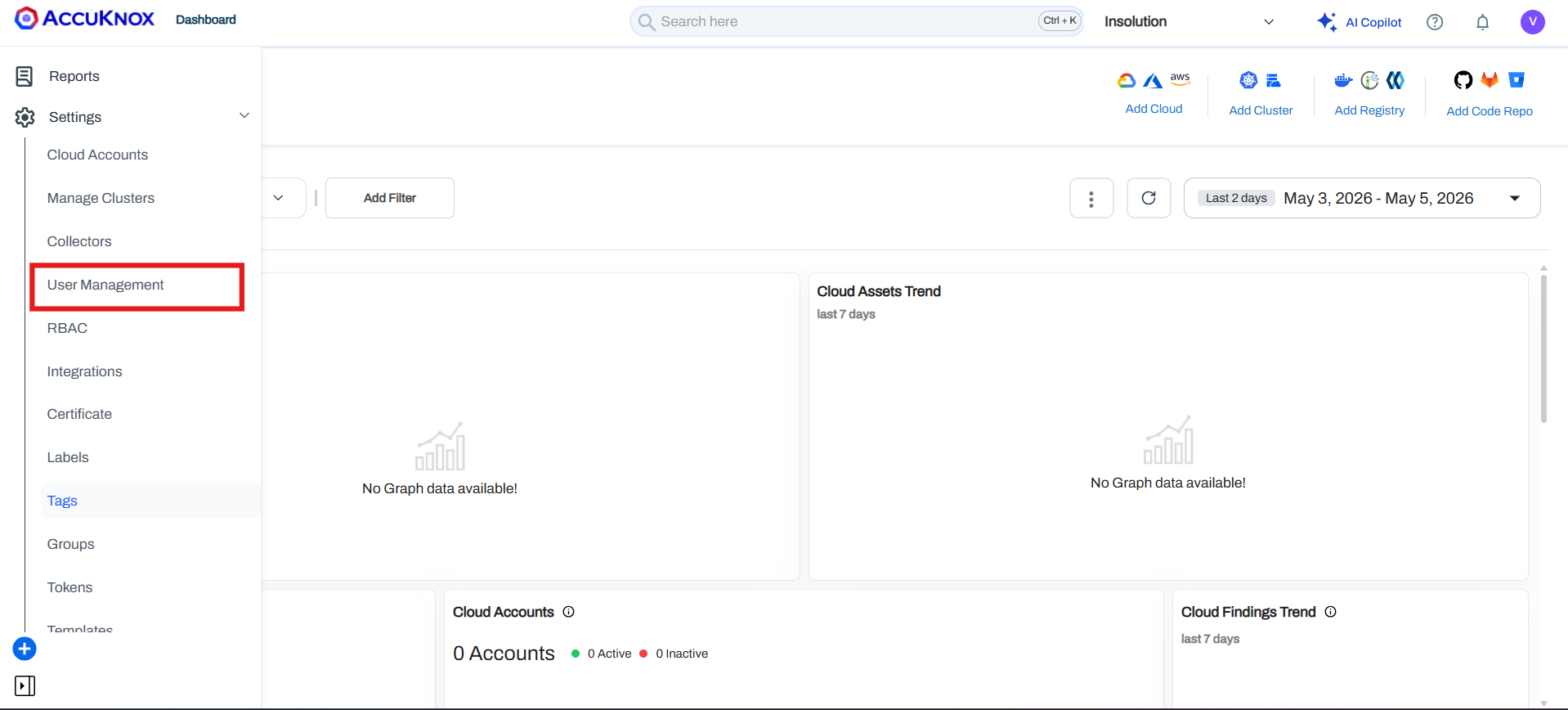
-
Click on your user profile.
-
Click the three-dot icon (⋮)
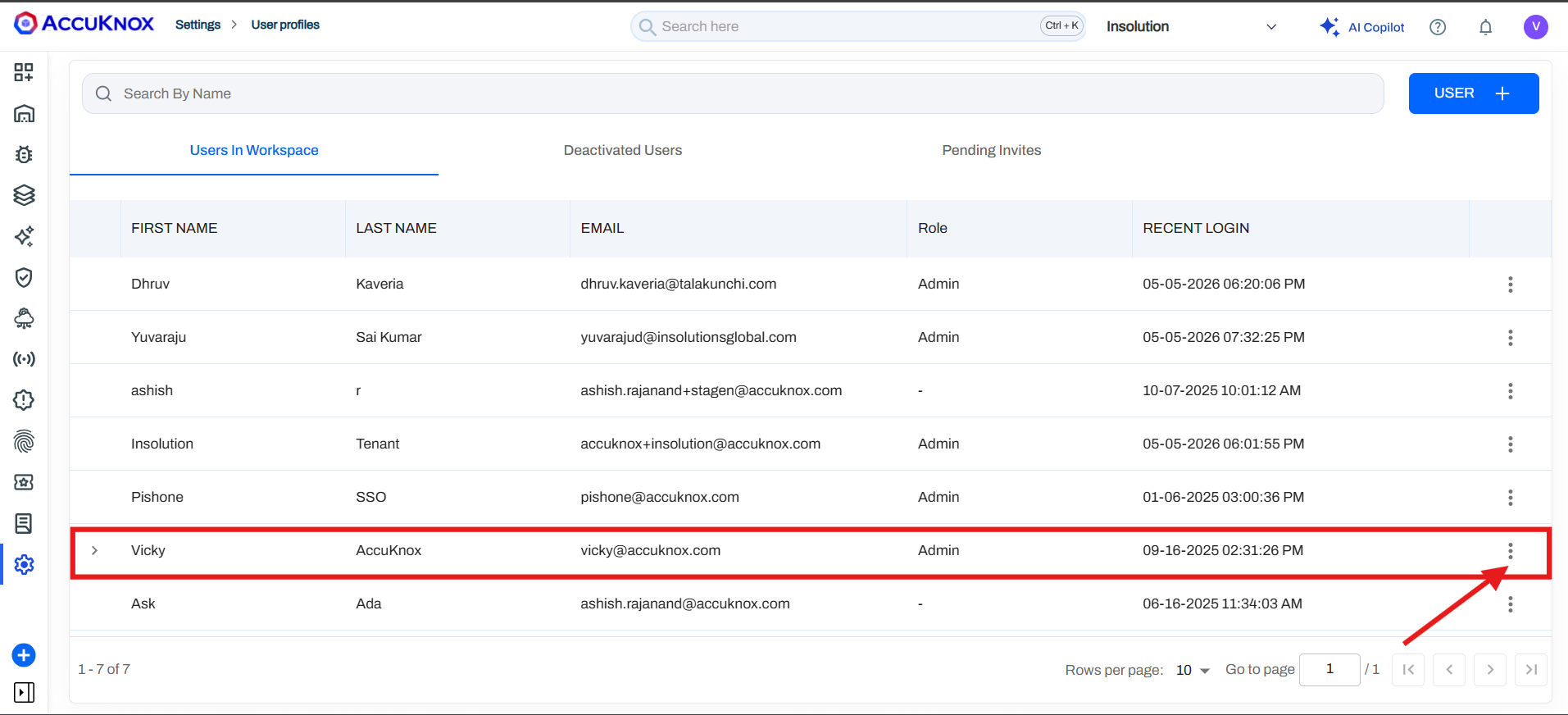
-
Select Create Access Key
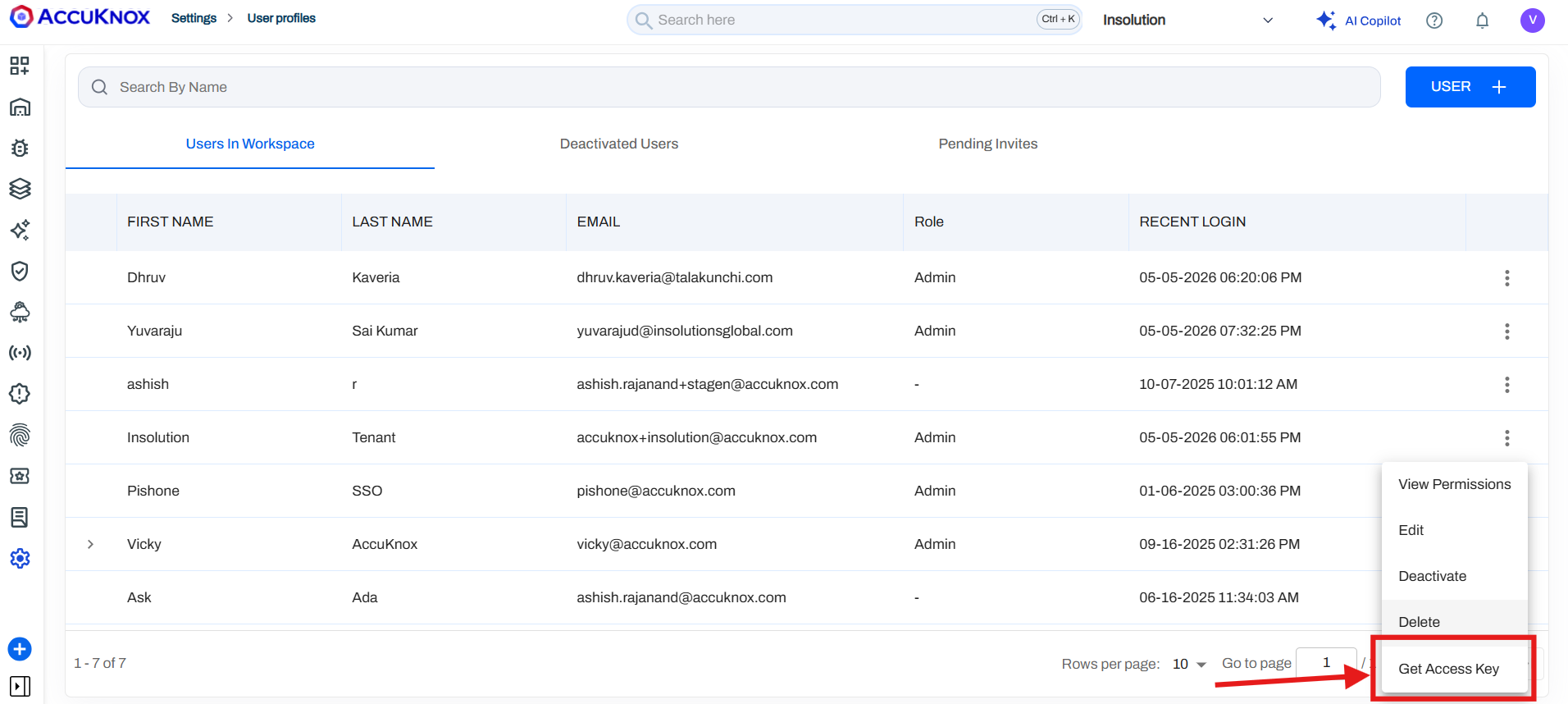
-
Copy the access key and save it securely
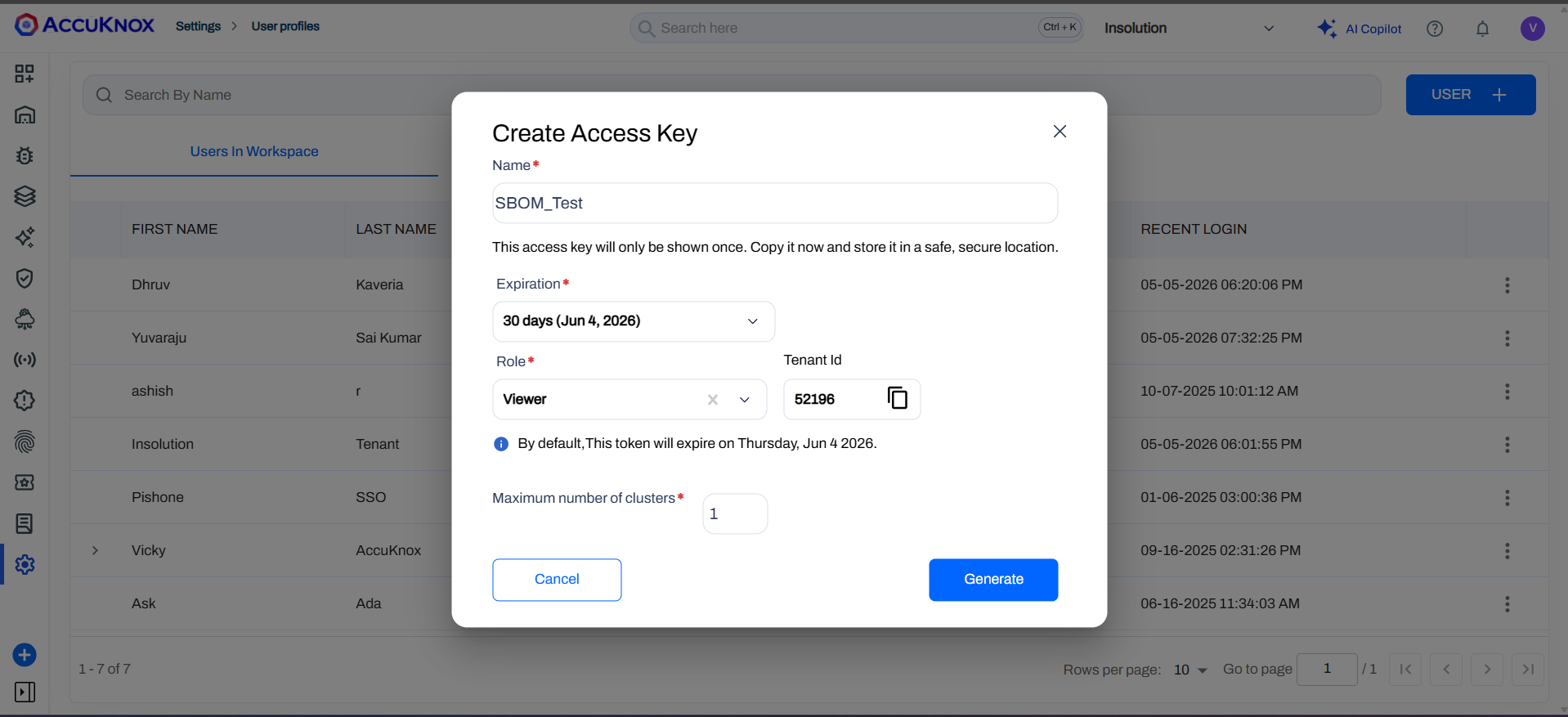
Note
You'll need this key for API authentication in the next steps.
Reference: How to Create Access Keys
Step 4: Run knoxctl (Windows)¶
Open your terminal and verify the installation:
./knoxctl.exe -h
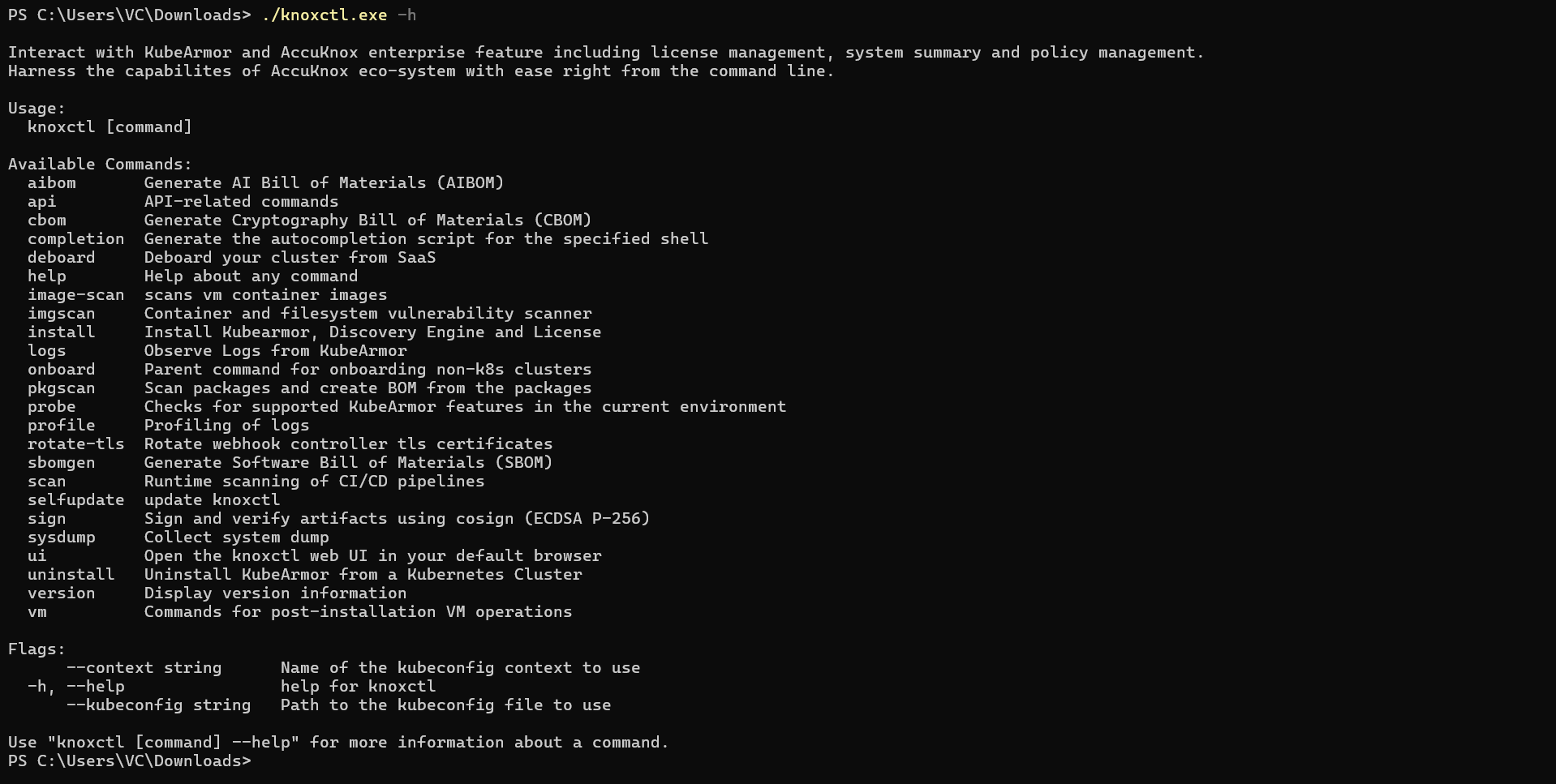
This displays available commands and options.
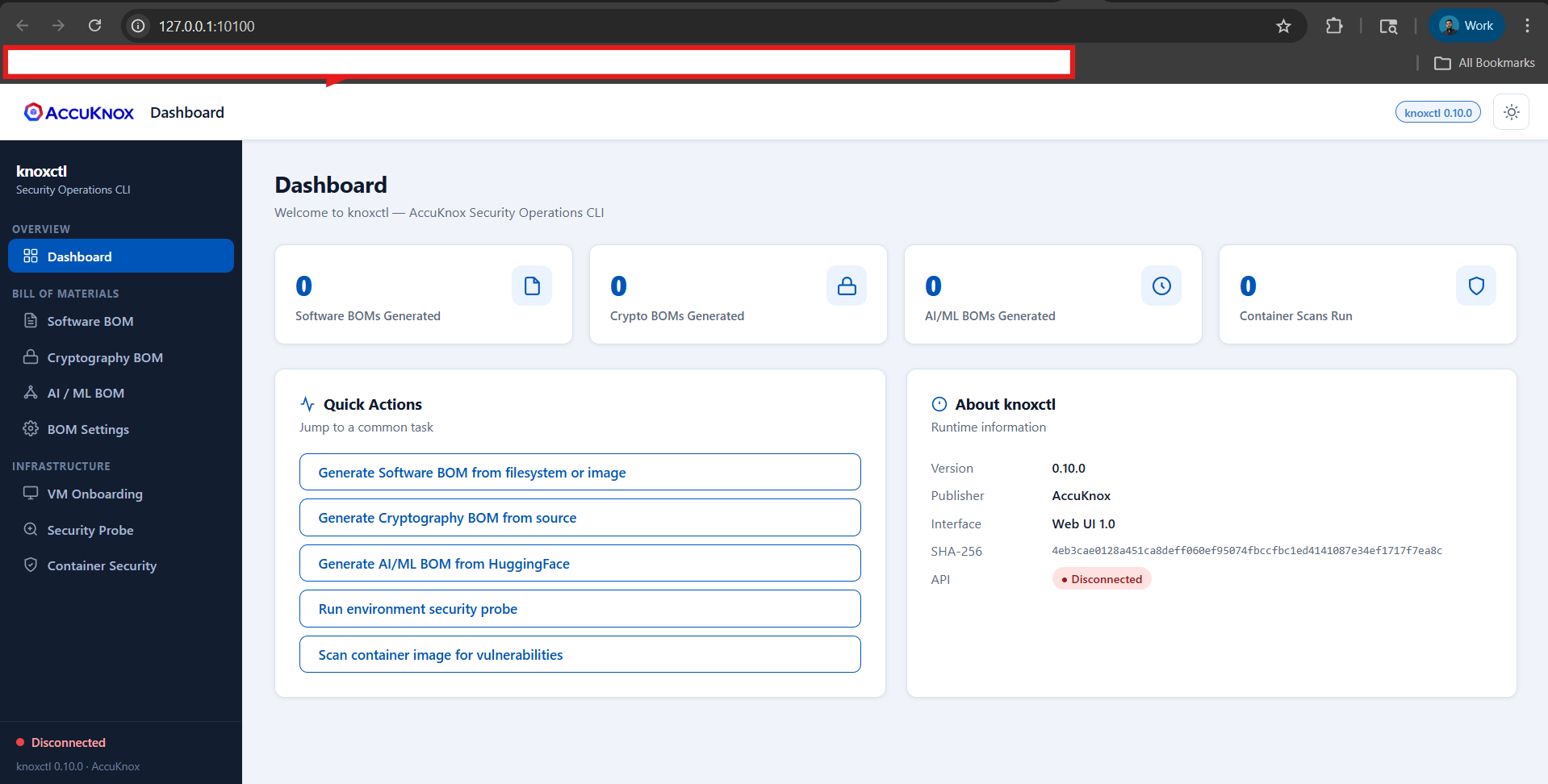
Step 5: Launch knoxctl UI¶
Start the local UI server:
./knoxctl.exe ui
The UI will be available at:
Open either URL in your browser.
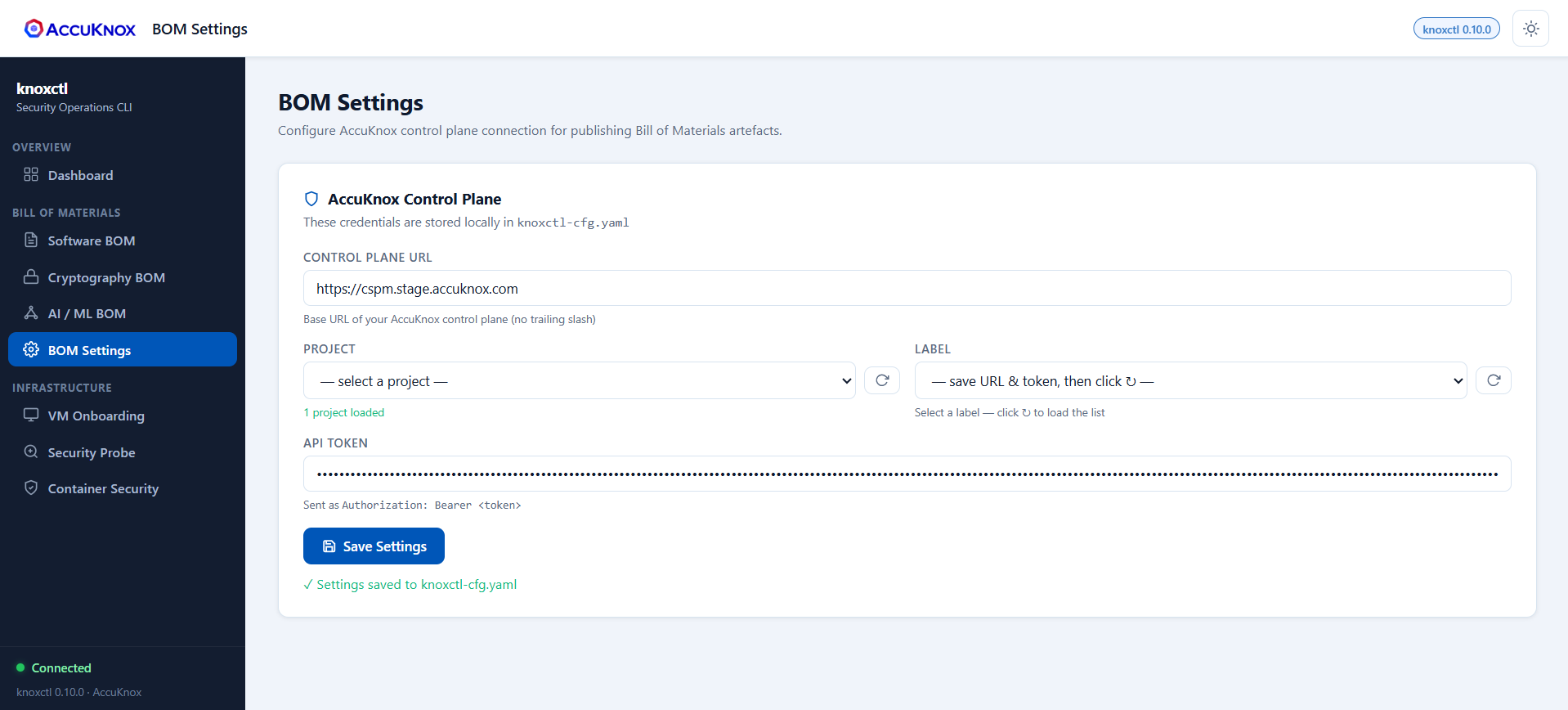
Step 6: Configure BOM Settings¶
In the knoxctl UI:
- Navigate to BOM Settings.
-
Add the following configuration — Control Panel URL:
https://cspm.stage.accuknox.comAPI Token: Paste the access key you created in Step 3.
-
Click Save Settings
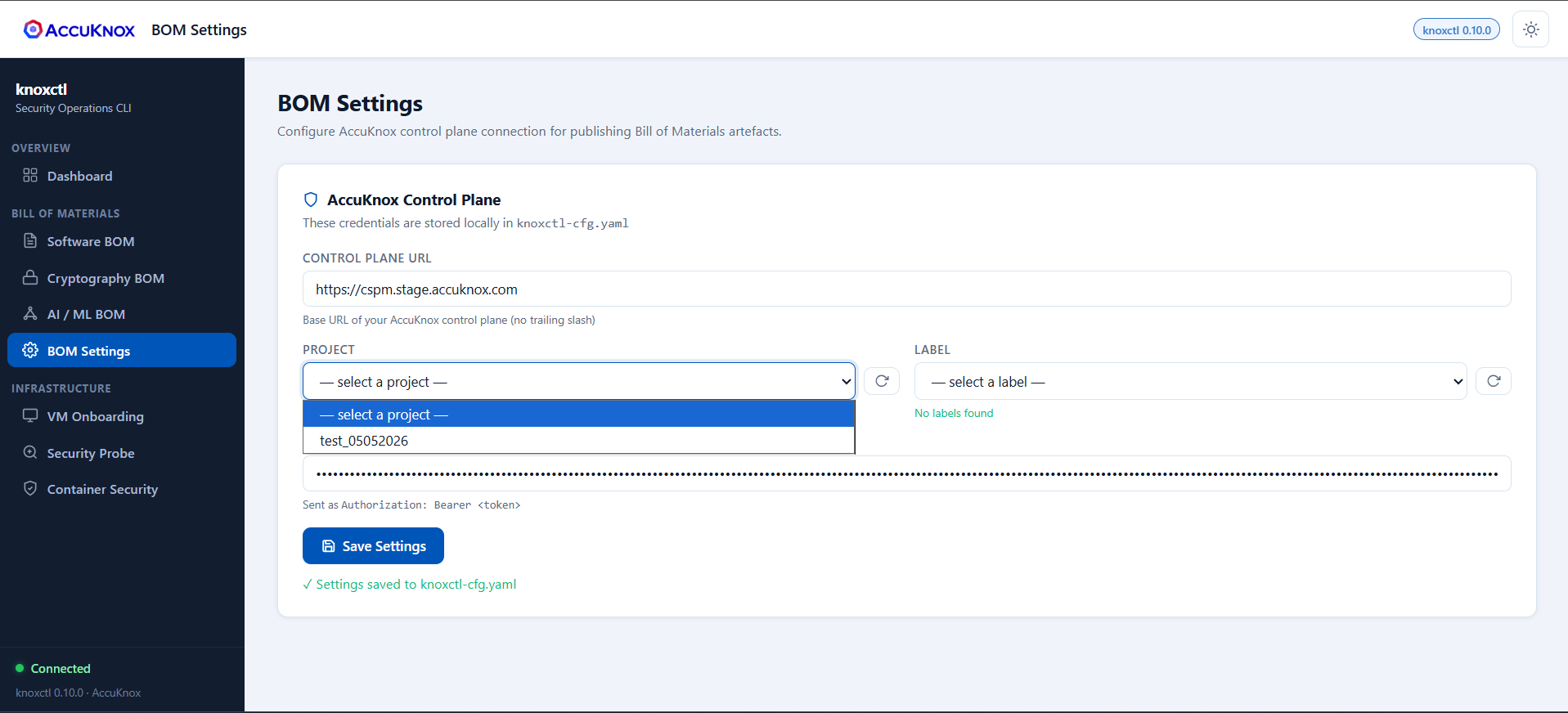
Step 7: Sync Projects and Labels¶
- Click Refresh for projects and labels.
- The UI will display all projects available on your tenant.
-
All associated labels will be visible.
BOM File Generation¶
After completing the setup steps, you can generate different types of BOM files based on your needs.
Additional options available in all BOM types:
- Sign artifact with cosign (ECDSA P-256): Optional checkbox to cryptographically sign the generated BOM.
- CLI Preview: The UI displays the equivalent
knoxctlcommand for your configuration, useful for automation.
Generate SBOM (Software Bill of Materials)¶
In the knoxctl UI:
- Navigate to Software Bill.
-
Configure the following settings:
- Source: Path to your project folder
- Output Scheme: Select the output schema
- Exclude Pattern: (Optional) Add any patterns to exclude
-
Click Generate SBOM
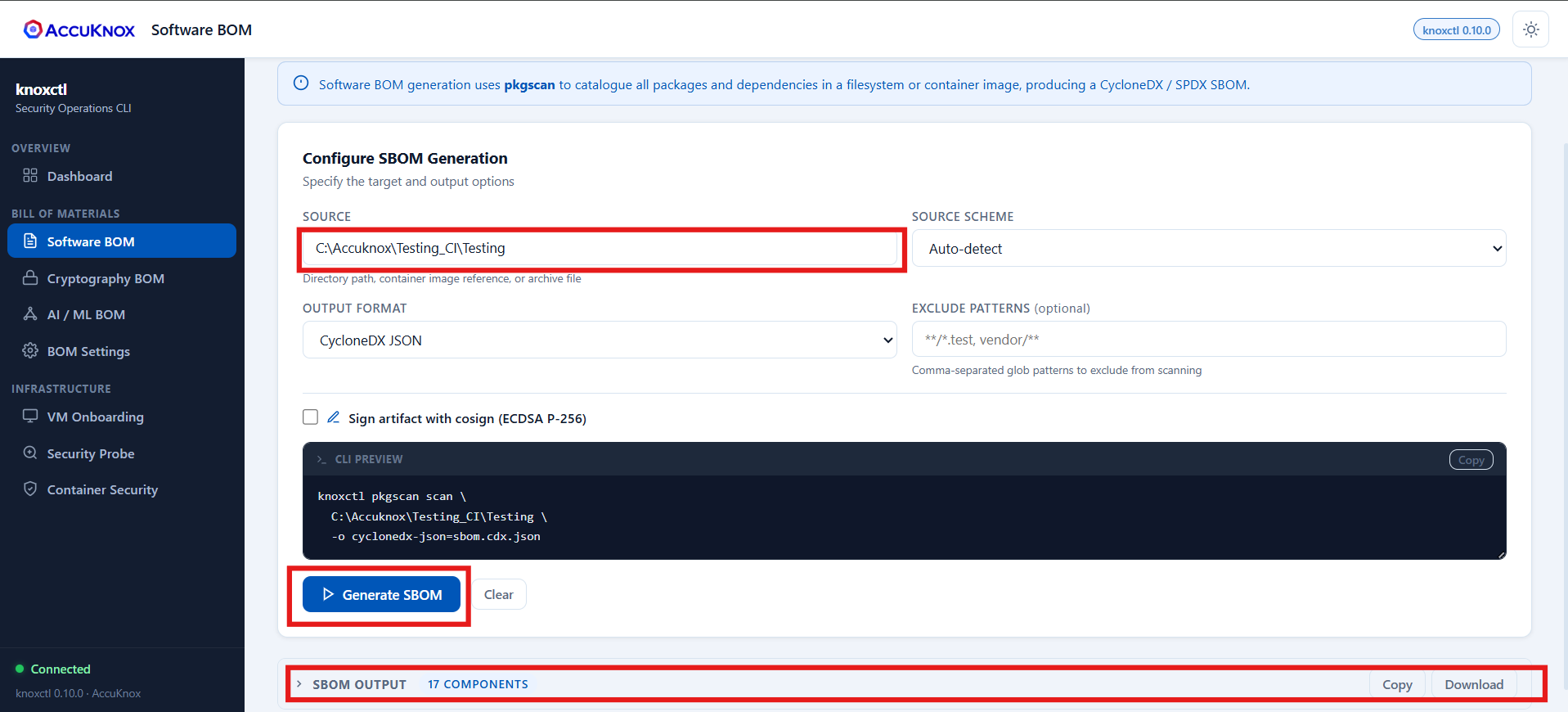
-
Download the generated file from the interface.
-
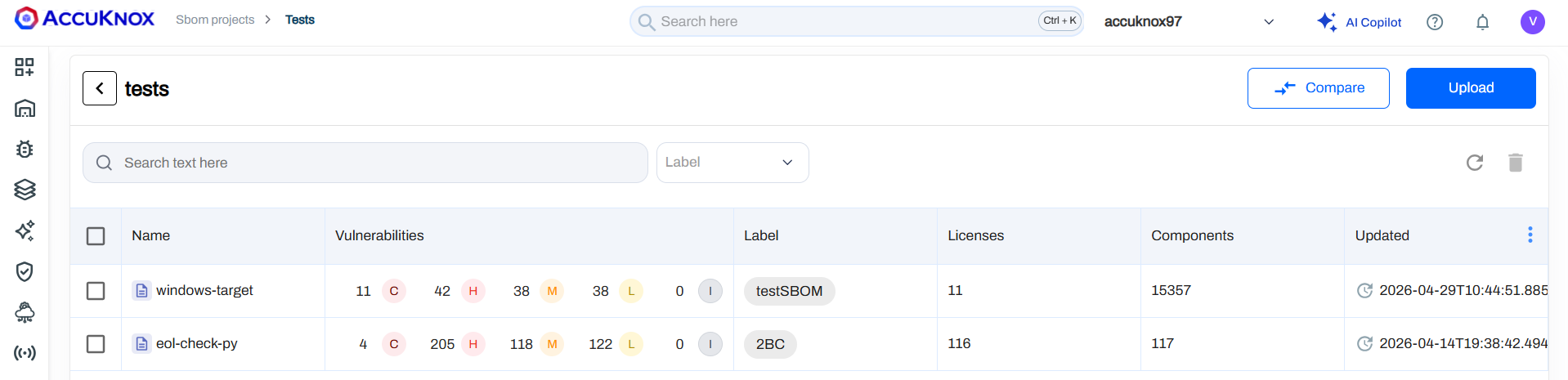
The generated SBOM will also appear in the UI under SBOM > Projects > [Your Project Name].
Generate CBOM (Cryptographic Bill of Materials)¶
CBOM can be generated for either filesystem projects or container images.
In the knoxctl UI:
- Navigate to Software Bill.
- Select Source Code as the scan type.
-
Configure the following settings:
- Source Path: Path to your project folder
- Project Name: (Optional) Name of your project
- Group / Module: (Optional) Specify group or module
- Version: (Optional) Project version
-
Click Generate CBOM
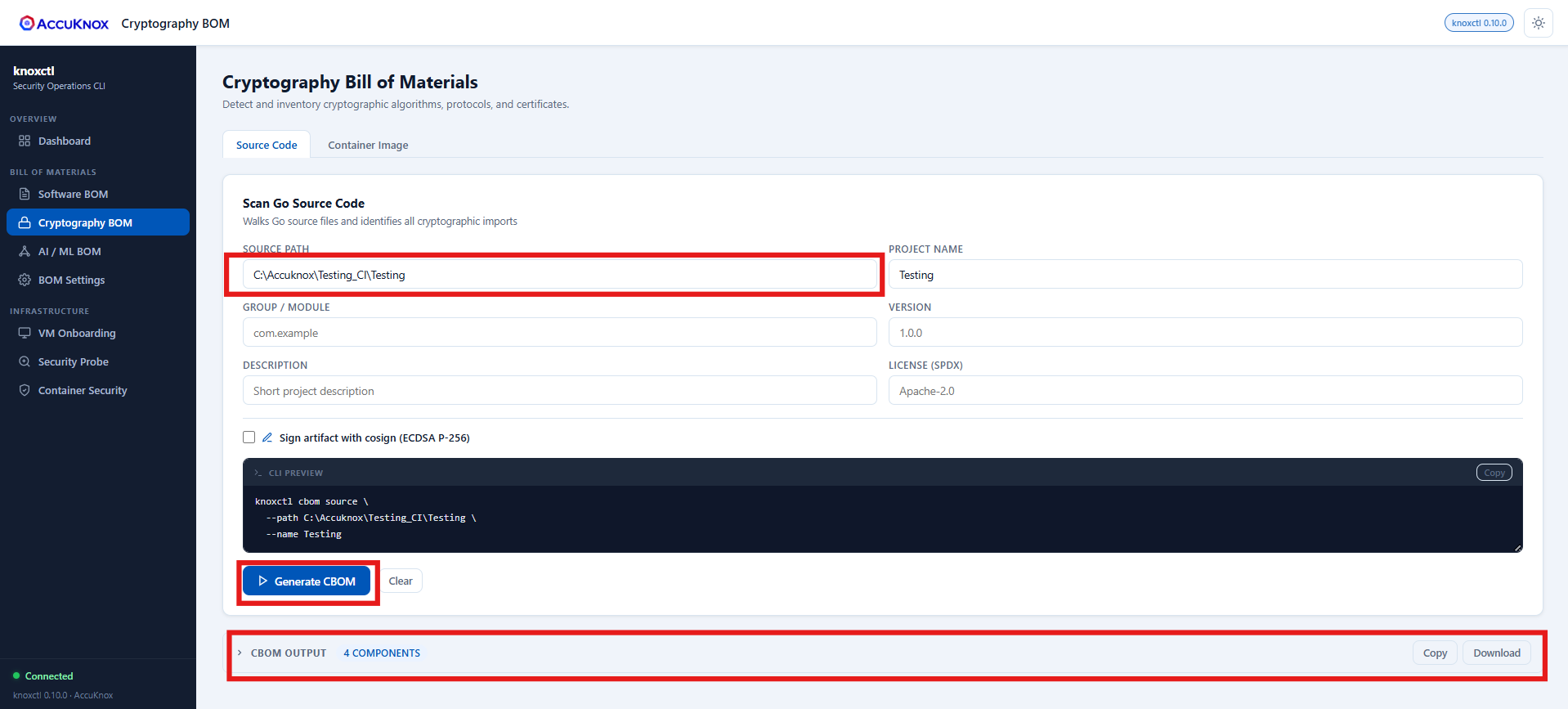
-
Download the generated file from the interface.
- The generated CBOM will also appear in the UI under SBOM > Projects > [Your Project Name].
Generate AIBOM (AI Bill of Materials)¶
Option 1: Hugging Face Model Scanning¶
In the knoxctl UI:
- Navigate to Software Bill.
- Select Hugging Face as the source type.
-
Configure the following settings:
- Model Identifier: Format:
owner/model-name(e.g.,meta-llama/Llama-2-7b) - API Token: (Optional) Hugging Face API token
- Override Name: Custom name for the model
- Override Version: Custom version identifier
- Manufacturer: Model manufacturer/creator
- Model Identifier: Format:
-
Click Generate AIBOM
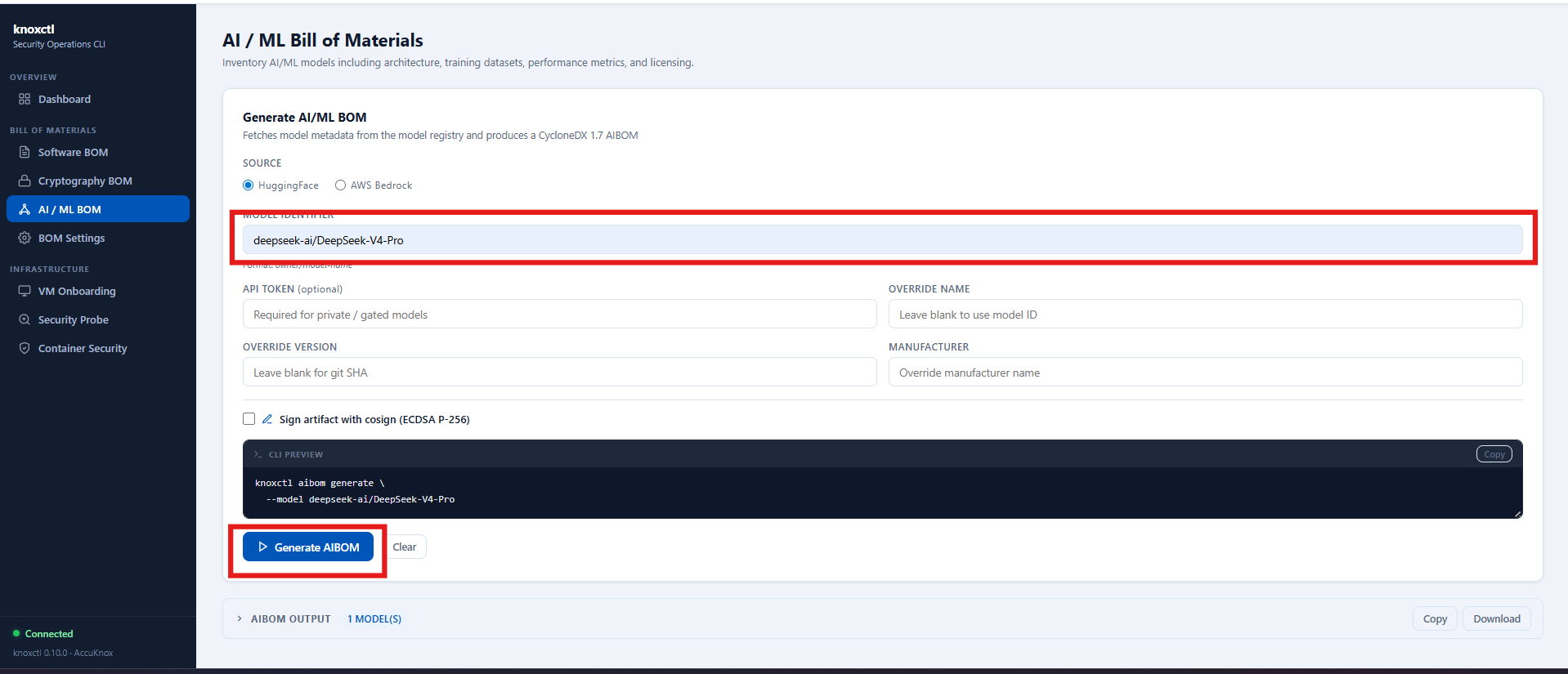
-
Download the generated file from the interface.
- The generated AIBOM will also appear in the UI under SBOM > Projects > [Your Project Name].
Option 2: AWS Bedrock Model Scanning¶
In the knoxctl UI:
- Navigate to Software Bill.
- Select AWS Bedrock as the source type.
-
Configure the following settings:
- AWS Region:
us-east-1(or your preferred region) - Model ID Filter: (Optional) Leave blank for all models
-
Credentials: Choose one of the following:
- Use Default Credential Chain (if AWS credentials are already configured in your terminal)
- Default chain: env vars →
~/.aws/credentials→ IAM role
- Default chain: env vars →
- Custom Keys:
- Access Key ID:
AKIAIOSFODNN7EXAMPLE - Secret Access Key:
wJalrXUtnFEMI/K7MDENG/bPxRfiCYEXAMPLEKEY - Session Token: (Optional) Temporary session token
- Access Key ID:
- Use Default Credential Chain (if AWS credentials are already configured in your terminal)
-
Override Name: Leave blank to use model ID
- Override Version: Leave blank for git SHA
- Manufacturer: Override manufacturer name
- AWS Region:
-
Click Generate AIBOM
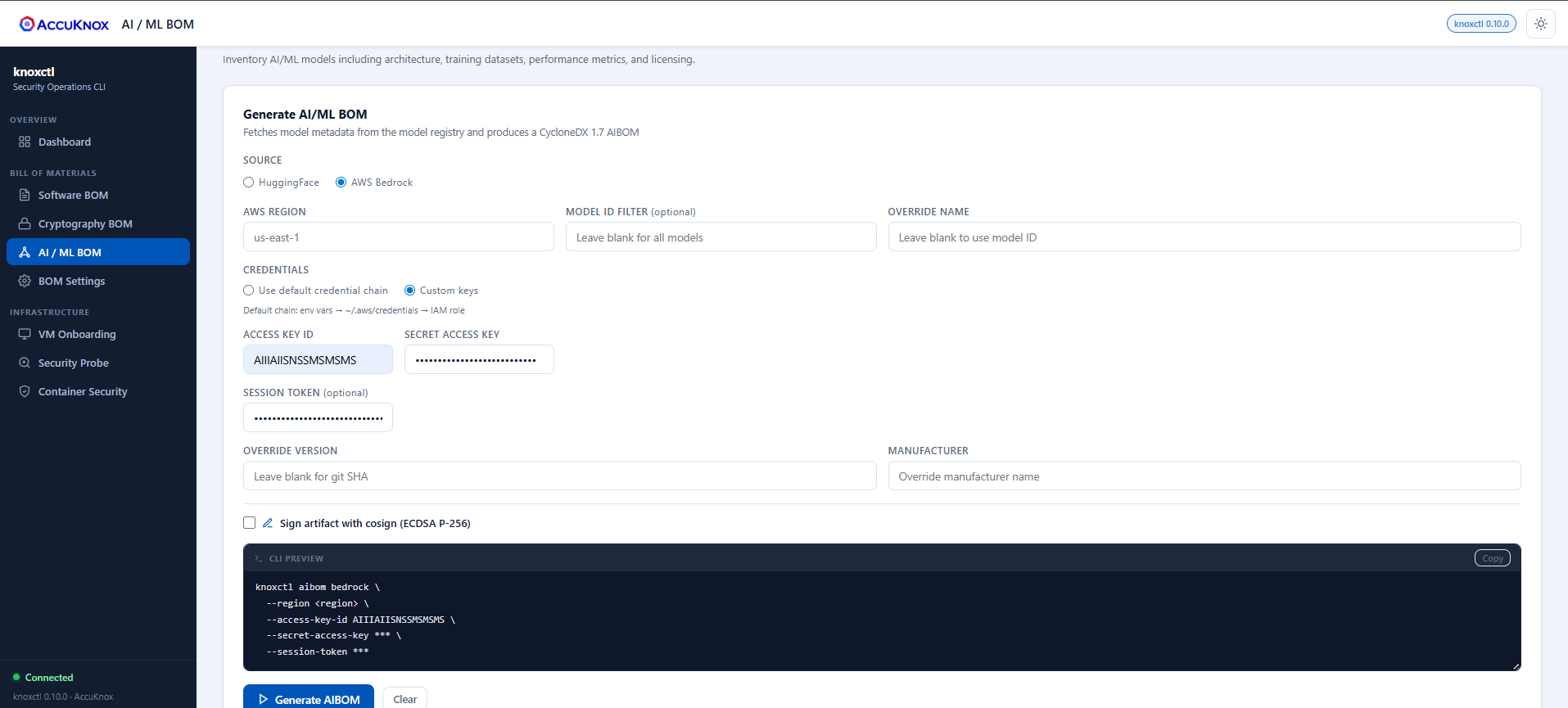
-
Download the generated file from the interface.
- The generated AIBOM will also appear in the UI under SBOM > Projects > [Your Project Name].
Generate SBOM via GitHub Actions (CI/CD)¶
If you prefer an automated CI/CD approach, AccuKnox provides a GitHub Actions integration that scans container images and generates SBOMs on every push or pull request.
Additional prerequisites:
- GitHub repository with a
Dockerfile - GitHub Secrets configured:
ACCUKNOX_TOKEN,ACCUKNOX_LABEL,ACCUKNOX_ENDPOINT
Setup¶
-
In AccuKnox UI, navigate to SBOM > Projects and create a project (see Step 1 above). The project name must exactly match the
project_namevalue in your workflow file.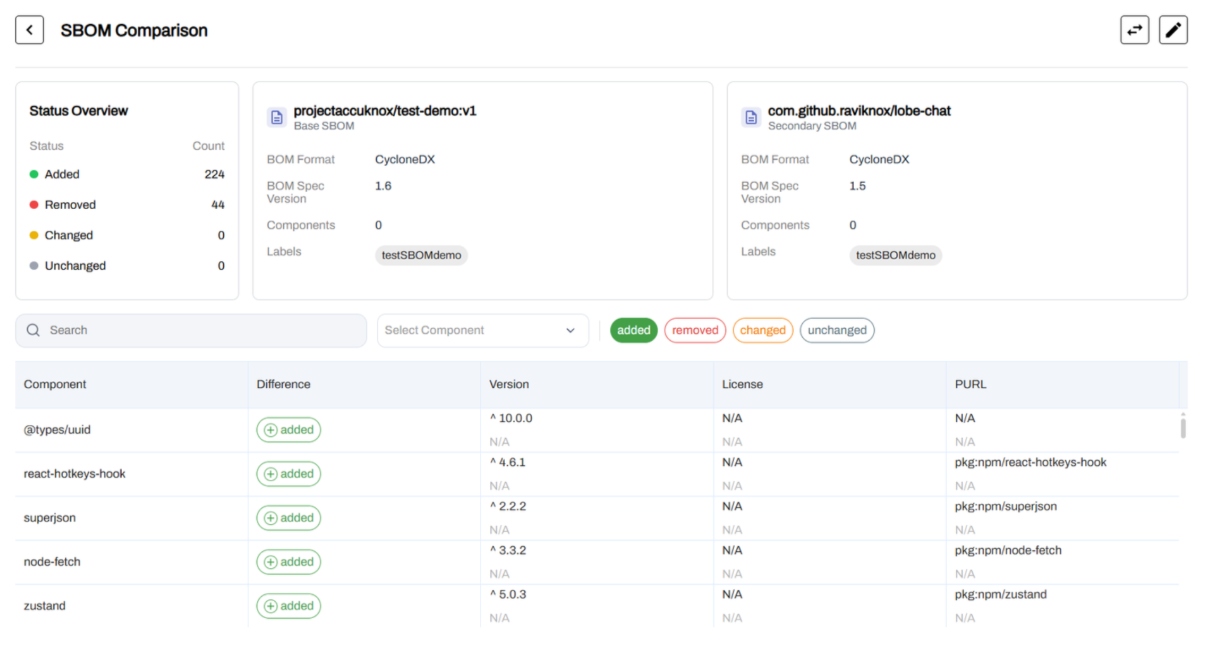
-
Click Add Project and fill in the project name, classifier (e.g., Container), description, and tags.
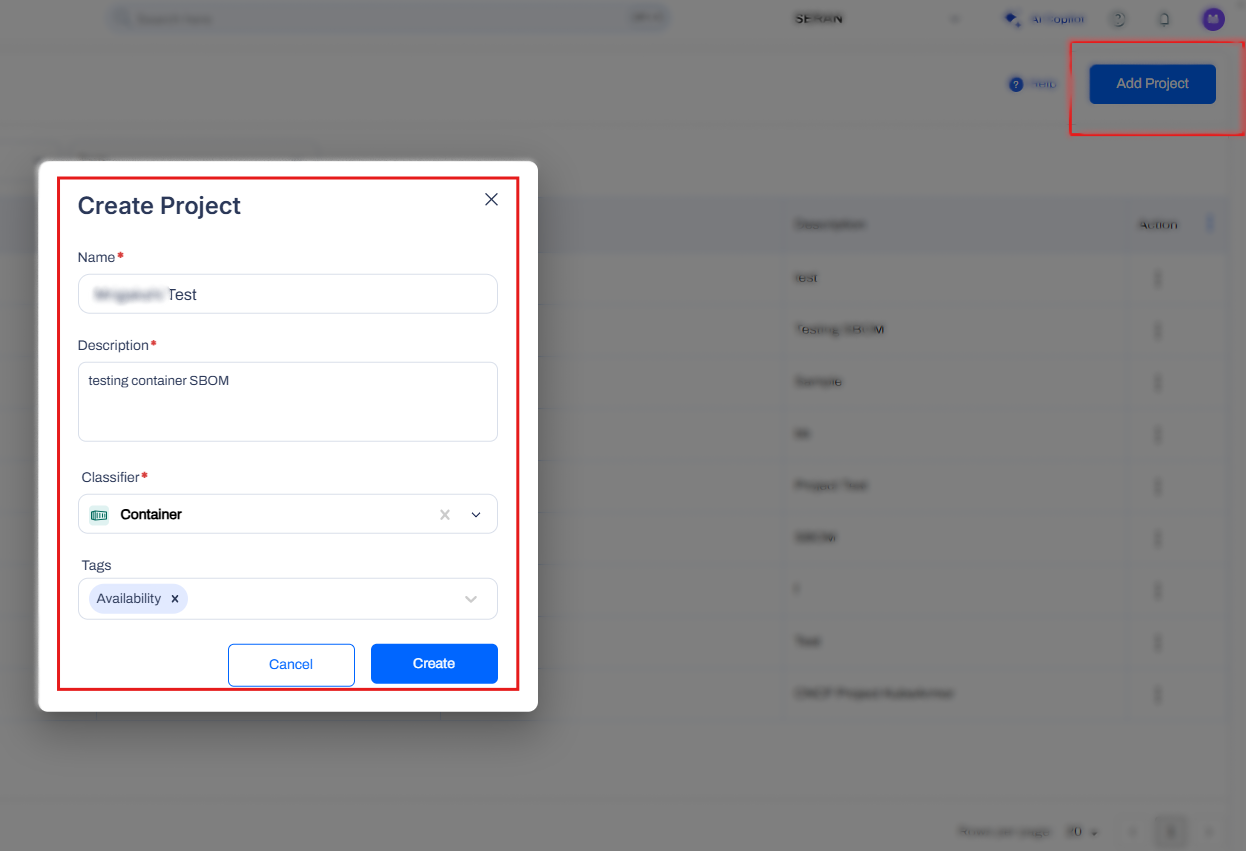
-
In your GitHub repository, create
.github/workflows/containerscan.yml:
name: AccuKnox Container Scan Workflow
on:
push:
branches:
- main
pull_request:
branches:
- main
jobs:
Container-scan:
runs-on: ubuntu-latest
steps:
- name: Checkout repository
uses: actions/checkout@v4.0.0
- name: Run AccuKnox Container Scanner
uses: accuknox/container-scan-action@latest
with:
accuknox_token: ${{ secrets.ACCUKNOX_TOKEN }}
accuknox_label: ${{ secrets.ACCUKNOX_LABEL }}
accuknox_endpoint: ${{ secrets.ACCUKNOX_ENDPOINT }}
image_name: "test-nginx"
tag: "latest"
severity: "UNKNOWN,LOW,MEDIUM,HIGH,CRITICAL"
soft_fail: true
upload_results: true
generate_sbom: true
dockerfile_context: Dockerfile
project_name: "Project Test"

-
Push changes or open a pull request to trigger the workflow.
-
Review results:
-
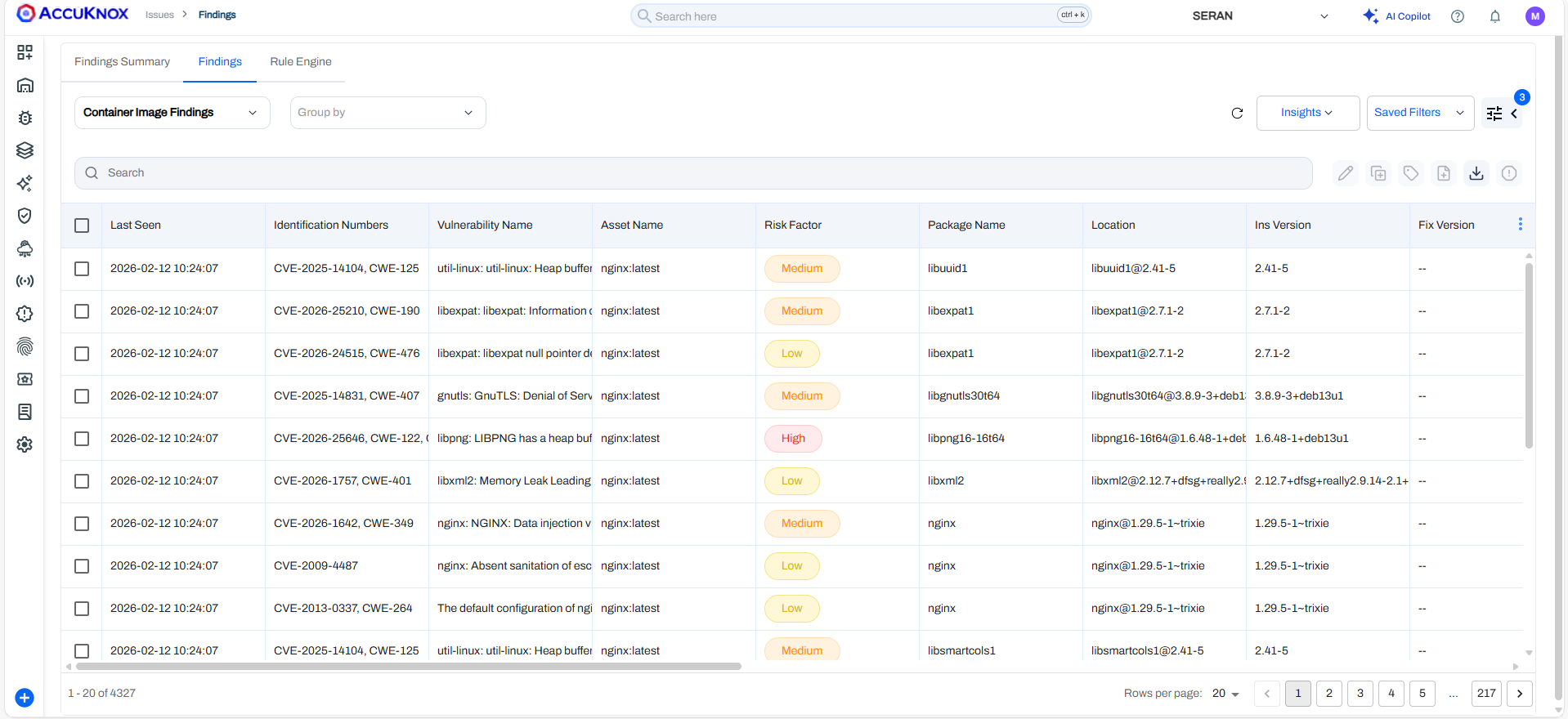
Findings > Issues Page for container image vulnerabilities.
-
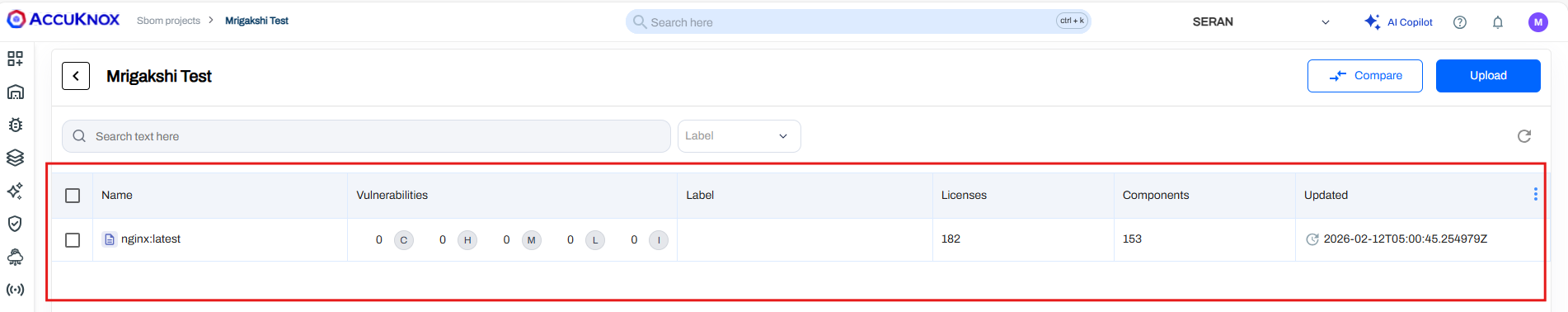
SBOM > Projects > [Your Project Name] for SBOM results and comparisons.
-
Sample repository
Fork containers/image to test this workflow with a real container image.
Post-Generation Workflow¶
Once generated, BOMs automatically appear in your SBOM dashboard, where AccuKnox scans them for known CVEs, license issues, and outdated components. View vulnerability details, track remediation, and export reports under SBOM > Projects > [Your Project Name].